Post Menu and Details.
- Your Business Data Has Been Compromised
- Question 1 - Has the attack occurred?
- Question 2 - What is the extent of the compromise?
- Question 3 - What to do to control the attack?
- Question 4 - How to prevent any future attack?
- Question 5 - Should you communicate the breach?
- Questions to Ask After Business Data Breach
- Questions to Ask When Your Business Data Has Been Compromised FAQs
Words: 1016
Reading time: ~4 minutes
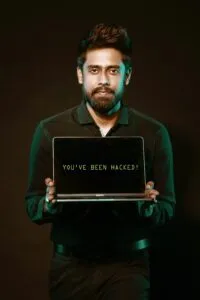
Here you will find questions to ask when your business data has been compromised.
In 2014, the media dug out a serious wind of the data breach, which severely affected more than a few large organizations. The one attack affected approximately seventy million people in America. During this attack, it was not just the organizations’ and individuals’ financial data, which was compromised, such as the credit card numbers, CVV codes, and expiration dates, but also the personal details such as the individual’s name, address, and phone number.
Your Business Data Has Been Compromised
One of the most common misconceptions that most people have is that only large corporations fall victim to hackers, says Dan, who offers the best product management courses. Well, let us explain to you why this misconception exists. It is because these are the only types of security breaches that we hear in the news.
However, both small, as well as mid-sized businesses must consider data breaches a severe threat. The risk only aggravates if the company has not made an adequate investment towards antivirus software and IT security.
Now, the big question that may strike your head is, why do the cybersecurity criminals attack the medium or even the small scale businesses? Well, a big reason for this is that many of these small or medium-sized organizations are partners and suppliers in the larger corporate entities.
So, when cybercriminals attack these smaller entities, it becomes their pathway to the larger partners. Another big reason that small or medium businesses become a target for hackers is because of their lack of adequate protection. Following a survey, it was found that there is approximately sixty-five percent of small businesses do not do enough to protect their data.
Of course, taking the necessary precautions can protect the business, but being hacked is still an ongoing risk, says FineGrades manager Subrat Sagar.
So, what to do if your business experiences a hacking incident? How do you overcome it?
Here, we are listing out five questions that you need to ask following a cyberattack.
 Question 1 – Has the attack occurred?
Question 1 – Has the attack occurred?
One of the biggest challenges that most businesses experience is identifying whether a hacking attack has occurred or not, says Berth, who offers online do my homework services with a reputed platform, TAE.
Unfortunately, in a few cases, the businesses might take a year to identify the data breach. So, how do you detect the problem right away? Be aware of the warning signs.
Some of the warning signs that you should keep a tab on are:
- Slow running systems or machines
- Strange patterns of network usage.
- Heightened crashes of the device
- Visits from an unfamiliar IP address
- An unusually high degree of data transfer to an unknown destination
Question 2 – What is the extent of the compromise?
After the attack has been identified, the next thing to do is find out the extent of an attack. So, how many machines or systems have been affected by the attack? For this, you need to hire a cyber-security expert. You would not want to aggravate the risk of increasing the scope and reach of the breach. It will only deteriorate the problem. A data security expert holds the power to identify the type of attack undertaken by the hacker. He will be able to do a malware analysis and a network analysis, which will help one figure out which data files or systems have been compromised the most.
So, this is the time you get the professionals involved.
Question 3 – What to do to control the attack?
Well, you may want to, but never pull the plug as soon as you find out that the data has been compromised. After you have understood the breach’s scope, you need to take measures to contain this attack. For this, the first step is taking all the systems offline.
Next, you need to wait for a thorough investigation to be conducted. This will help you determine ways to protect the system from future attacks.

Question 4 – How to prevent any future attack?
Once all the systems have been taken offline, you need to install or reinstall the antivirus in each of them. Next, take adequate measures to fill in the security gaps, which caused the attack. Frank, an IT manager with TFTH, says that many data breaches happen because of risky employee behavior.
Well, it is true. The risk employee behavior includes – opening suspicious emails, visiting unsafe websites, or clicking insecure banners.
To avoid this, you will need web filtering services and firewalls.
Question 5 – Should you communicate the breach?
Well, the simple answer to this is 100% YES. Of course, companies get hacked, but that does not mean that it is catastrophic. You need to plan and seek ways to communicate the attack to the primary stakeholders, partners, employees, and customers.
Depending upon the type of data compromised, you also have a legal obligation to communicate the same to your consumers. Consult digital media, copyright experts, or entertainment lawyers for potential risks and legal actions you can take. The individual law varies from one state to another. So, it is best to be aware of your legal responsibilities well in advance. If you believe that you may never be able to overcome the hack’s impact, be transparent and honest about it. Communicating the issues helps strengthen the trust between the clients and the businesses.
However, ensure that you are making efforts to prevent a future attack.
Questions to Ask After Business Data Breach
So, we fully explained in this article what to ask and what to do when you feel your business data has been compromised. Follow this list and you will manage it:
- 1 – Has the attack occurred?
- 2 – What is the extent of the compromise?
- 3 – What to do to control the attack?
- 4 – How to prevent any future attack?
- 5 – Should you communicate the breach?
Questions to Ask When Your Business Data Has Been Compromised FAQs
Where can I get business data?
1. Crunchbase
2. AngelList
3. Data.gov
4. Google Finance
5. Social Mention
6. Glassdoor
7. Lending Club
8. The Kauffman Index of Startup Activity
Is business analytics the future?
Is. it is. Right now many businesses need a business analytics
Do business analysts make good money?
Yes it is because business analysts are demanded work
Thank you for reading!


 Question 1 – Has the attack occurred?
Question 1 – Has the attack occurred?