Post Menu and Details.
- What is Snowflake Data Warehouse?
- Benefits of Snowflake in businesses
- Challenges involved with row-based security
- Advantages of Satori over Snowflake
- Snowflake Column Level Security
- Limitations of column-level security in Snowflake
- Conclusion
- Data Warehouse Security Best Practices FAQ
Words: 1189
Reading time: ~5 minutes
In the recent past, setting up a data warehouse involved a lot of money, especially designing the hardware appliances and running them in the personal data center. Contrary to most of the methods used earlier, Snowflake data warehouse service is a software as a service (SaaS) method which has cut down expenses.
What is Snowflake Data Warehouse?
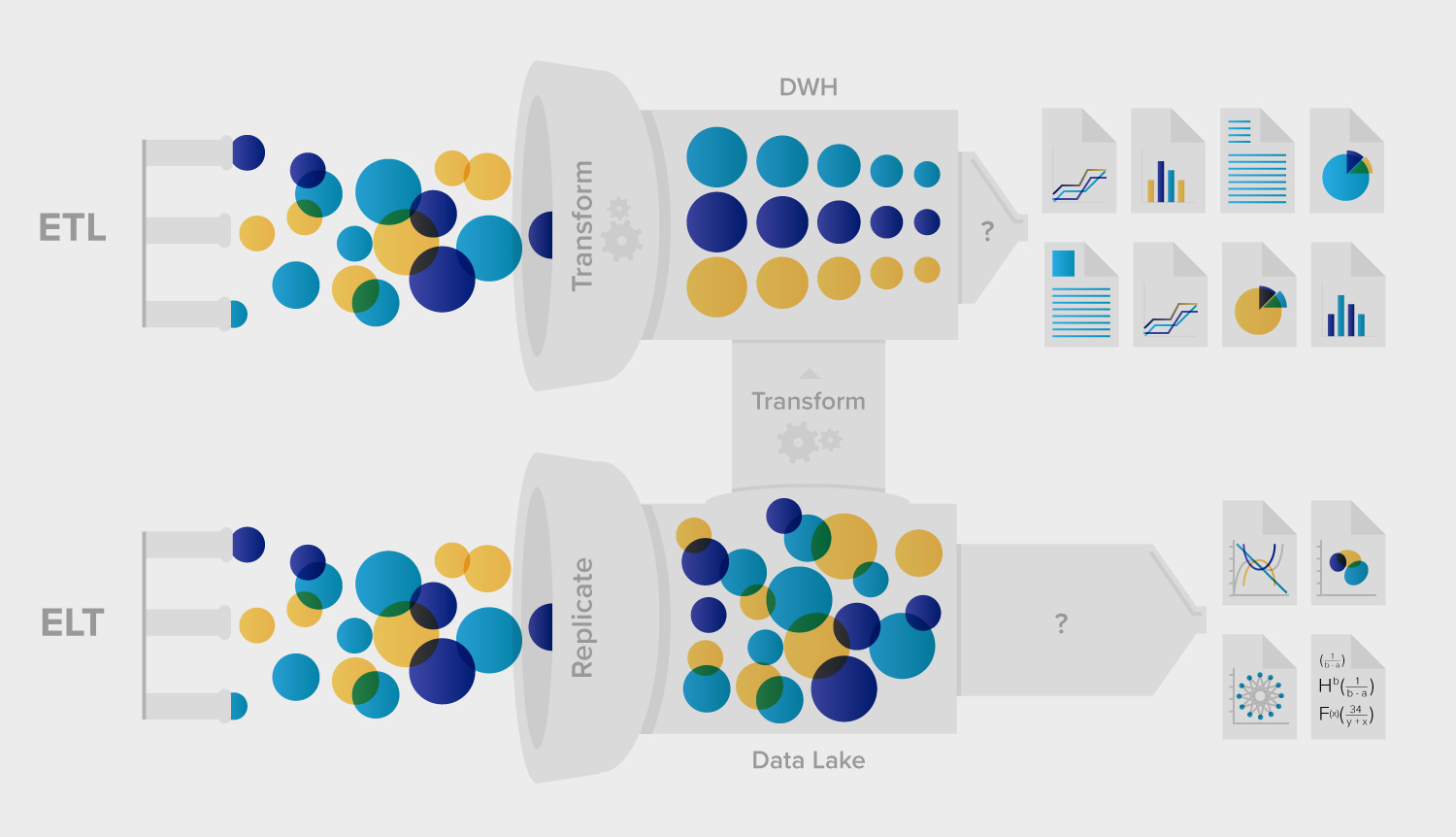
Snowflake simply encompasses a data warehouse built on top of the Amazon Web service or sometimes on Microsoft Azure cloud infrastructure. It does not have separate hardware or software for selection, installation, or configuration, making it ideal for all data organization. Moreover, Snowflake does not require any maintenance and support resources. Also, it allows you to quickly move your data in it using a switch like a device called ETL solution. This guide will cover topics under Snowflake concerning its benefits to consumers such as businesses, the components of Row Level access control, and finally, column-level security.
For the most part, Snowflake is designed to help solve problems present in older data warehouses that are hardware-based, for instance, delays and failures, limited scalability, and issues surrounding data transformation. As a result, Snowflake has benefited a lot of businesses extensively.
Benefits of Snowflake in businesses
1. Enhances speed and performance
The Snowflake is elastic in nature, meaning that you can load as much data as possible and enjoy the advantage of extra compute resources in it. Afterward, you can scale your virtual warehouse down and only pay for the time you used.
2. Storage and support
The storage layer of Snowflake is divided into structured and semistructured layers. The cloud automatically manages all the aspects of data and dictates how to store the data. Snowflake allows the user to load structured and semistructured data into the cloud without analyzing or transforming it. This is because it will automatically optimize how the data storage and querying are done.
3. Concurrency and accessibility
Delays and failures are common challenges faced in a traditional data warehouse with many users. This is because a large number of users poses too many queries to compete for fewer resources. However, with Snowflake, this is a different case because of the availability of its multicluster architecture. Snowflake receives questions from one virtual warehouse as a separate case and will never mix them with other queries from a different virtual data warehouse. Also, every virtual warehouse that loads its queries can scale up or down as required.
Data analysts and scientists do not have to wait for loads of data to complete processing but get their results when they need it.
4. Security and availability
Snowflake is distributed equally between the platforms in which it operates, whether Azure or AWS. It is created in such a design that it can tolerate all the network failures without impacting the customers. It is certified by SOC 2 type II with more levels of security. Some of the additional securities include support for PHI data and network communication encryption.
6. Data sharing
This cloud allows for data sharing among the Snowflake users. Moreover, organizations can also share data with data consumers whether they are using Snowflake or not by creating a reader account from their user interface. With this functionality, you can create as well as manage this cloud account for your consumers.
6. Snowflake Row Level Access Control
This is also called row-based security. It is a concept used in data access control whereby your access to data in a table is restricted to certain conditions, individual users, different groups, and roles with additional permissions. Also, it is based on the identities found in that particular rows. With the right conditions in place, this can be your best data protection control system. This has been implemented by businesses, especially when an organization has a table containing sales data for different departments supposed to be viewed by a few teams. The Row-level access control will ensure that only the right teams retrieve the data in their department.
Challenges involved with row-based security
Explicit row-level security: This means in an attempt to allow users to retrieve data on their specified regions, somehow, the process fails, and users end up accessing data of several regions.
Implicit row-level security: This has some settings in it that limit the user from receiving all the data they are supposed to given the available access control settings. In this case, the user does not have to do any filtering, but still, a filter will be added.
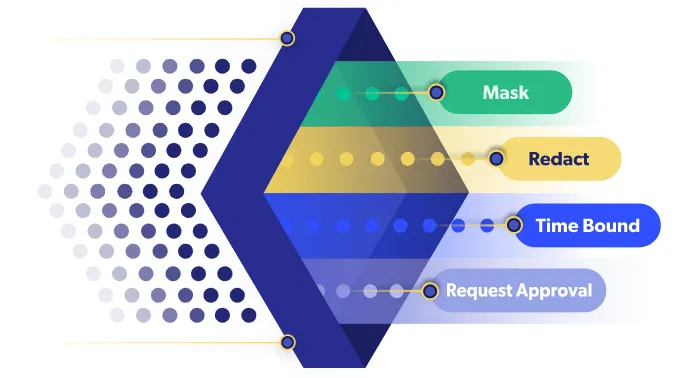
With these challenges and other limitations in Snowflake, some people will decide to use Satori row-level security. Satori, unlike Snowflake, simplifies data access by setting up policy controls. The data processed by Satori has tags from this cloud, such as PCI and PII.
Satori manages to disintegrate security controls from infrastructure data so that policies do not require much knowledge about the data.
Advantages of Satori over Snowflake
- The system of security used increases the user’s technology independence.
- The system allows the user to set enormous data security controls.
- It has the identity context from your identity provider
Snowflake Column Level Security
Column level security works more like row-level security except that it sets the kind of data you can access and the columns you can access. This is important for business because it allows respective individuals to access data belonging to their departments. It is implemented in two ways; explicitly and implicitly.
When this is implemented implicitly, users who go ahead and query columns they don’t have access to will view empty columns. On the other hand, explicit access control will allow the users to query only the columns they have access to.
Limitations of column-level security in Snowflake
- It is tricky to manage access with overlapping roles or where both rows and columns are used for security.
- The use of secure views hinders performance.
- It involves a long process of defining policies and views.
Conclusion
To sum up, Snowflake is among the industries providing people with leading features in terms of data security. With its many features such as dynamic data masking and end to end data encryptions, Snowflake allows its users to focus on other issues surrounding data, such as analyzing instead of protecting. It provides the users with a service that is secure and resilient, enabling their demanding data workloads.
Bonus video: Database VS Data Warehouse
Data Warehouse Security Best Practices FAQ
How do you secure a data warehouse?
To secure data in the warehouse, you should follow these rules:
- Set read-only by default
- Restrict IP addresses that can connect to the Data Warehouse
- Set Custom Roles to with only needed permissions
- Do monthly account audit and cleanup
What security concerns should be considered in building a data warehouse?
There are 3 main data security concerns – Confidentiality, Integrity, and Availability (CIA).
What factors should be considered while designing a data warehouse?
Here are the main factors to consider while designing a data warehouse:
- The Choice of Data Warehouse.
- ETL or ELT. *
- Flow.
- Accessibility.
- Space.
* ETL is the Extract, Transform, and Load process for data.
* ELT is Extract, Load, and Transform process for data.
What are the basic elements of data warehousing?
The basic elements of data warehousing are:
- A central database
- ETL tools*
- Metadata
- Access tools
* ETL is the Extract, Transform, and Load process for data.
Thank you for reading!

![Data Warehouse Security Best Practices [snowflake]](https://jealouscomputers.com/wp-content/uploads/2021/01/Data-Warehouse-Security-Best-Practices-Snowflake-1024x472.webp)